Chainloop provides a centralized platform for artifact management, real-time visibility, and automated compliance for your Software Delivery Process.
Get started
If you’re new to Chainloop, you can get started using the guides below.
Quickstart
Get started with Chainloop in minutes.
Getting Started Guide
A step-by-step guide to will walk you through many of the Chainloop features.
Concepts
Learn about the key concepts of Chainloop
Deep dive Guides
Guides to help you get the most out of Chainloop.
If you are interested in project compliance, don’t miss the following guides.
What’s Chainloop?
Chainloop provides a centralized platform for artifact management, real-time visibility, and automated compliance. It bridges gaps between Developers, security, and compliance teams.
Some of Chainloop’s pillars include.
Central Evidence Store for SDLC: A single platform to centralize, connect, and validate any evidence or metadata —from SBOMs and IaC validation reports to SAST, DAST results, and cloud security checks. The collection of data

Change Management: We offer a clear separation of concerns and communication channels between Dev, SecOps, and compliance teams, fostering seamless collaboration, communication, and productivity.

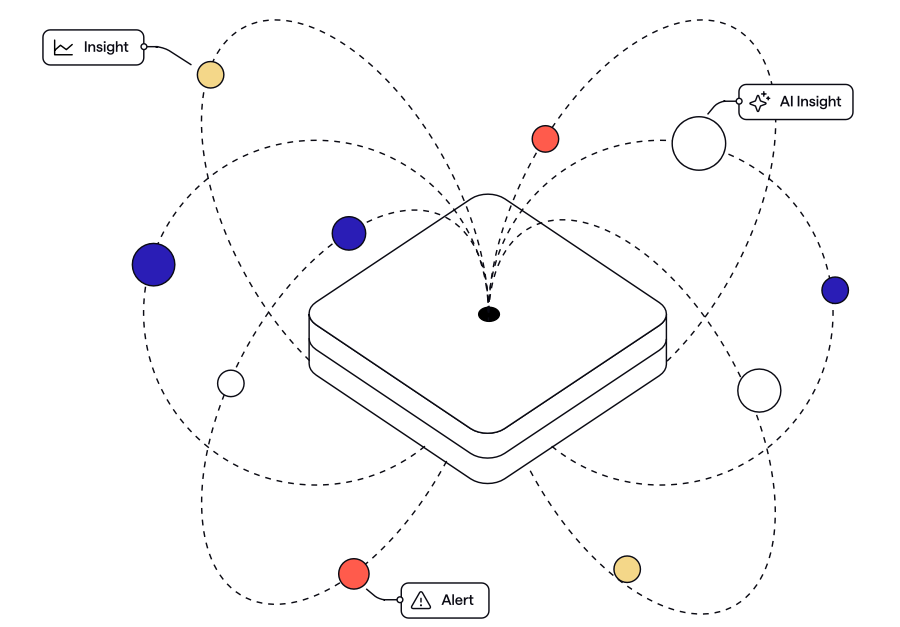
Visibility & Alerting: Real-time insights into SDLC security posture with proactive alerts.
Automated Compliance: Offer automated validation through customizable policies, frameworks, and requirements, reducing manual effort and improving accuracy for security and compliance.

How does it work?
You can learn more about the core concepts of Chainloop in the Concepts section.
With Chainloop, Security, compliance, and Risk management teams on the right, get a single pane of glass where they can define security and compliance policies, what evidence and artifacts they want to receive, and where to store them.
On the left, developers are shielded from all this complexity by being given simple instructions on what to provide when instrumenting their CI/CD pipelines.

Metadata Generation
Developers produce key data—such as build artifacts, SBOMs, vulnerability reports, and other compliance evidence—during the software build process.
Easy Integration
DevOps integrate Chainloop into existing CI/CD pipelines using our CLI or integrations, automatically capturing all the necessary evidence with context (e.g., Git commit details and pipeline configuration).
Digital Signing
Every piece of metadata is digitally signed (using SLSA, in-toto, sigstore, or your own PKI such as AWS KMS or Keyfactor) to ensure it is tamper-proof and verifiable.
Centralized Storage and Validation
Signed data is pushed to our secure evidence store, where it is validated and organized into a comprehensive record.
- Graph-Based Provenance: Every item is connected in a traceable graph, ensuring complete visibility over the software lifecycle.
- Immutable Storage: Artifacts are signed and stored immutably, providing a robust audit trail.
Automated Policy Enforcement
Security and compliance teams define rules using our curated policy library. These policies are automatically applied, delivering immediate risk assessments and remediation guidance.
Continuous Monitoring
Our system continuously checks that every project meets your defined security and compliance standards.
Real-Time Insights
An intuitive dashboard provides instant alerts and clear reports to keep your teams informed.
By turning complex security processes into a simple, automated routine, Chainloop helps you build and deliver trusted software faster.
Who is it for?
Enterprises comprise fragmented, siloed Software Supply Chain practices, and tools, making it difficult to introduce security and compliance requirements efficiently in their organizations. This slows down the Software Delivery Process or even blocks it under strict regulations in highly regulated markets, especially since Compliance and Risk Management (CRM) programs still rely on manual, costly, and slow processes.
At their core, most security and compliance initiatives, such as vulnerability management, license compliance, or self-attestation, involve making decisions or sharing metadata generated during the software delivery process. Metadata that ranges from Software Bill Of Materials (SBOMs), vulnerability scans, and QA reports to attestations or more.
As regulatory requirements like FedRamp, Executive Order 14028 in the US, and the EU Cyber Resilience Act (CRA) or Digital Operational Resilience Act (DORA), just to mention a few, continue to evolve, automating compliance on top of trustworthy metadata is no longer optional.

